Security Is More Than Encryption
There is a common and risky assumption in modern product development: "We use AES-256, so the device is secure." Encryption matters, but encryption only protects data in transit. It does not address compromised firmware, untrusted silicon, or supply chains you don't control.
Across defense and commercial markets, products are routinely marketed as "secure" even when the companies behind them do not write their own firmware, do not control manufacturing, and do not fully understand what their hardware is doing at the chip level. This gap is not theoretical—it's where modern vulnerabilities live.
In contemporary conflict and competition, compromise does not always arrive loudly. Sometimes it is kinetic, and sometimes it is silent—embedded in firmware, introduced through a component substitution, or hidden behind an undocumented interface that was never audited. Once deployed, those weaknesses propagate downstream, inserted directly into operational systems. Security, in this context, is not a feature, it's a system property.
Engineered for Trust Under Constraint
PATCH is designed with the assumption that it will be deployed in environments where infrastructure cannot be trusted and scrutiny is guaranteed. That assumption drives design across the entire system.
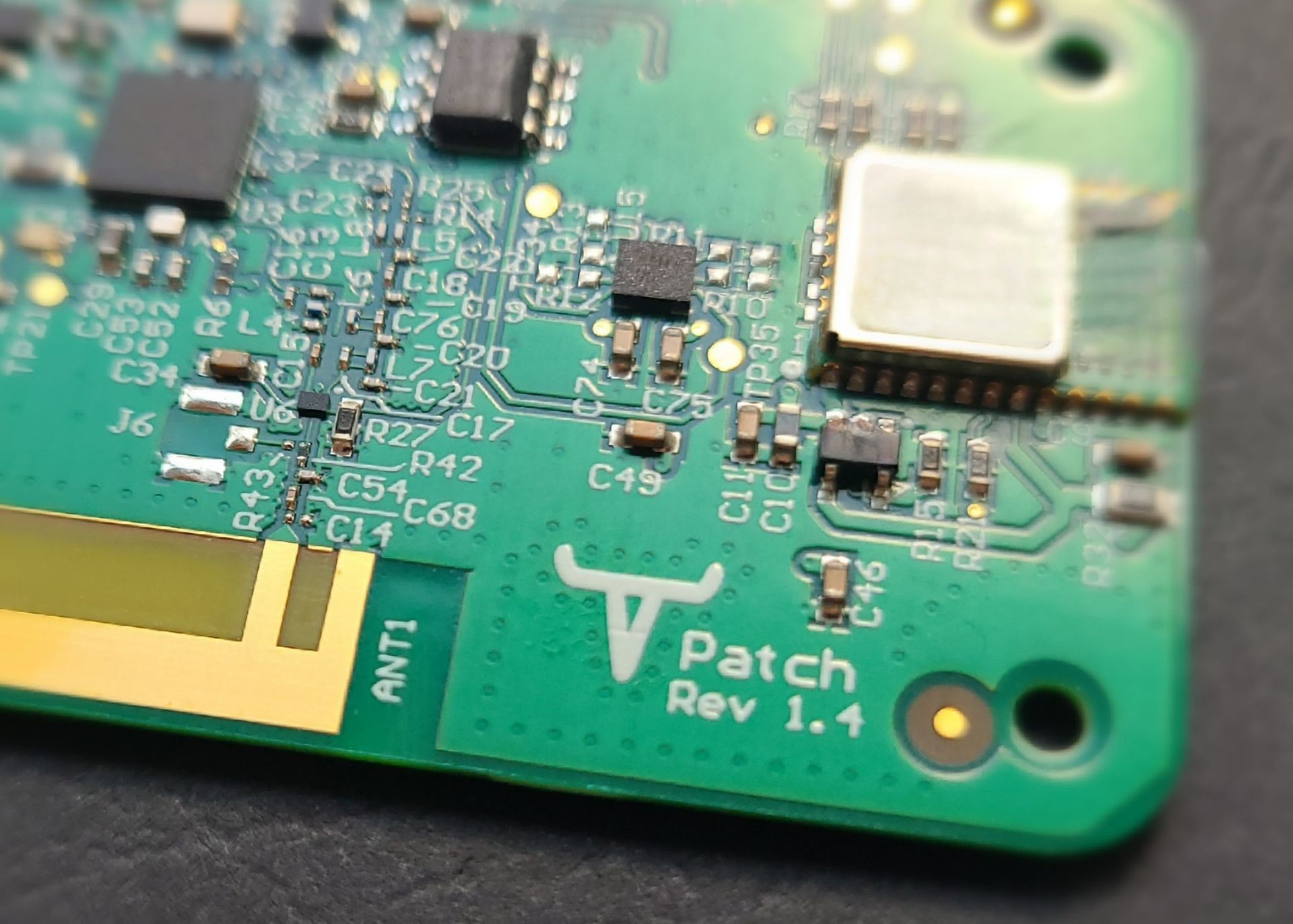
Roper is the original equipment manufacturer (OEM) for PATCH. Circuit board design, fabrication, programming, and device assembly occur in the United States under our direct oversight. All firmware and software, including the PATCH mobile application, are developed and maintained by our team of U.S. citizens. PATCH is fully NDAA-compliant.
The system is intentionally designed with a reduced attack surface:
- No Internet connectivity or IP-based networking
- No operating system (bare-metal firmware)
- No open-source code
- No physical ports or external interfaces
PATCH is designed with no persistent data storage. Location, activity, and message data are not stored on the device. PATCH uses our SnapMesh™ protocol, which ensures that encryption keys and network configuration data exist only for the duration of an active session and are wiped when the network is shut down or when a device loses power.
Data transmitted over SnapMesh is encrypted using AES-256 with a one-time-use key generated at network initialization. Communications between PATCH and a paired smartphone use Bluetooth Low Energy (BLE) Secure Connections with AES-128 encryption and ECDH key exchange (P-256), along with privacy measures to limit device tracking and correlation.
PATCH also monitors network integrity in real time. Replay attacks are detected and blocked, with users notified if an attack is detected while maintaining network operation. PATCH has been independently tested in the field to be resistant to jamming outside 277 yards.
Why This Matters
When hardware, firmware, manufacturing, and supply chain are treated as separate problems, weaknesses accumulate quietly. When they are designed together, security becomes a property of the system, not a claim. That is the difference between security as a feature and security as an outcome.


